I began the challenge at 1400hrs and worked constantly for 18 hours, by which time I had one root and two low privilege shells. Unfortunately this didn't change for the remainder of the challenge.
As a result, I failed.
Looking back, I realise a number of mistakes I made in tackling the challenge.
First of all, I got one root and two low privilege shells well within the first 5 hours. I then spent the next 17 hours going in circles, becoming more and more frustrated, more tired, clock watching and becoming more worried that I wouldn't pass.
This clearly isn't the best technique.
I have found that half of the challenge appears to be time management. I was determined to power through the sleep deprivation, believing that I could cheat the performance degradation that tiredness brings; as it turns out, I'm not super human.
The tiredness itself impacted my memory. I look back and realise that I was repeating the same (privilege escalation) steps over and over again, the definition of madness...
With the clarity and soberness of a rested mind, I look back and realise that I missed some significant and obvious clues. For what appears to be one reason: The challenge itself is difficult, and rightly celebrated for that fact. As a result, I believe I had convinced myself that it would require all of the enumeration-exploitation-privilege escalation-Fu that I could summon to master it. Now I'm sure an element of that is true, however I believe I missed a big portion of what is being tested: prioritisation, time management, effective and concise analysis.
I also realise I scripted too much. I read many blog posts and forum posts written by other students that had tackled the challenge, almost all of which featured a significant amount of scripting.
Of course, I have used custom scripts constantly throughout the PWK labs, however I decided to write a monster enumeration script of epic-ness especially for the exam, I think this was a mistake.
I had forgotten that in the labs I had popped some of the most challenging machines without the use of this script. I had thrown away a tried and tested methodology for an unproven enumeration script that did the 'analysis' for me.
Although my script helped me to quickly get low privilege shells on two machines, I had robbed myself of valuable human analysis that may well have given me the edge in later privilege escalation. For which, I payed the price.
So for my own peace of mind, and potentially to the benefit of others, here is a list of what I recommend:
[1] Develop a definitive time-line and stick to it. Limit the effects of tiredness and tunnel vision as much as possible.
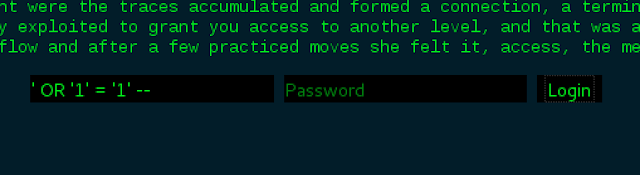
[2] Do not prejudge how technically difficult the challenge is. Pursue clues that you are given; don't dismiss them in the belief that it cannot be that simple.
[3] Do not repeat the exact same exploits/techniques expecting a different outcome, unless new information comes to light that changes the vector.
[4] Initial enumeration - exploitation - low priv shell - secondary enumeration - privilege escalation - root/system. It works. stick to it.
[5] Do not over script enumeration. Unless your coding up some immense machine-learning analytical script of awesomeness, no script can beat human analysis and pattern recognition.
[6] Enjoy the experience. Don't worry about failure. If I hadn't failed, I wouldn't know everything I've just written.
The OSCP challenge is, like the labs, a learning experience. Even though I am bitterly disappointed that I failed it this time; I know that it is making me a better penetration tester and that is very valuable indeed.